- Natively integrated
- Proactively prevent risks, actively stop threats, and reactively ensure unmatched business continuity across NIST.
- Easily manage and scale with a single platform and agent to deliver all cybersecurity, data protection, and endpoint management services.
- Ensure compliance and protect sensitive data with behavioral-based DLP and best of breed disaster recovery.
- Highly efficient cybersecurity
- Protect endpoints with visibility across the most vulnerable attack surfaces – incl. email, identity, Microsoft 365 apps.
- Streamline analysis guided by AI and unlock a rapid, single-click response.
- Improved performance on endpoints via a single agent for complete security: XDR, EDR, MDR, anti-malware and anti-ransomware, DLP, data protection, endpoint management and monitoring.
- Built for MSPs
- Unlock superior ROI via a centralized platform that streamlines daily tasks and reduces costs.
- A SaaS-based, multitenant platform with role-based access that’s easy to manage and scale across disperse client IT environments.
- Extend additionally with 200+ integrations, including commonly used by MSPs — SIEM, PSA, RMM tools.
- GovernRapidly establish cybersecurity and risk management strategies, set roles and policies, and ensure continuous oversight via an integrated platform.
- IdentifyIdentify vulnerable assets and data you need to protect across multiple endpoints.
- ProtectProactively protect IT assets, endpoint devices and data with integrated backup, DLP and endpoint management capabilities.
- DetectContinuously monitor via AI- and ML-based threat detection and behavioral analysis to guard against advanced threats and data exfiltration.
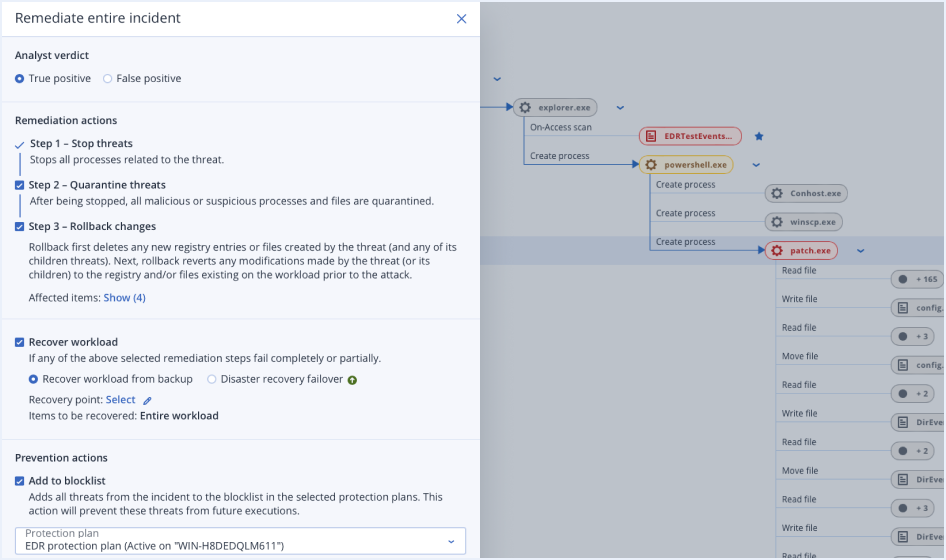
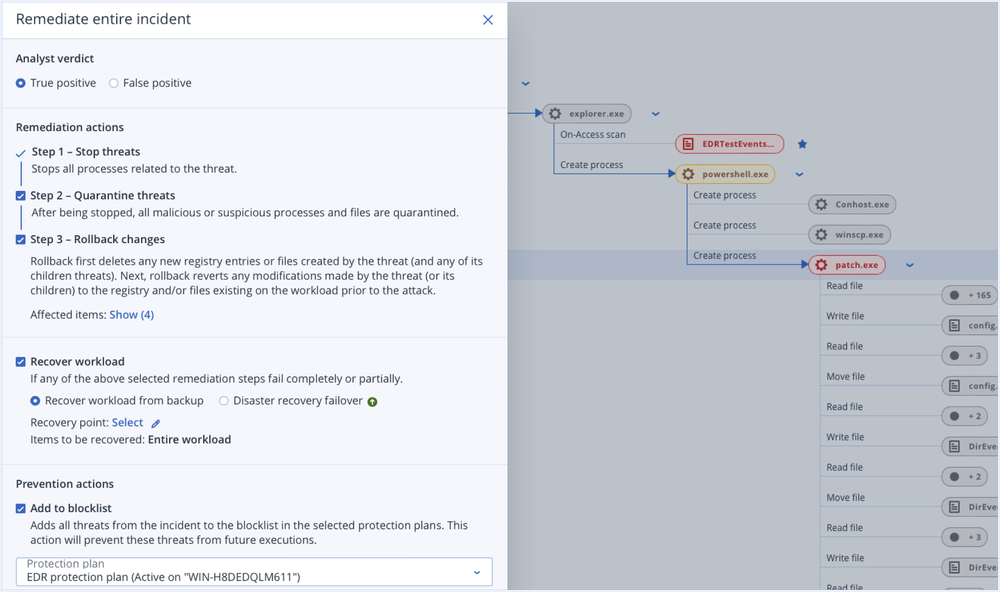
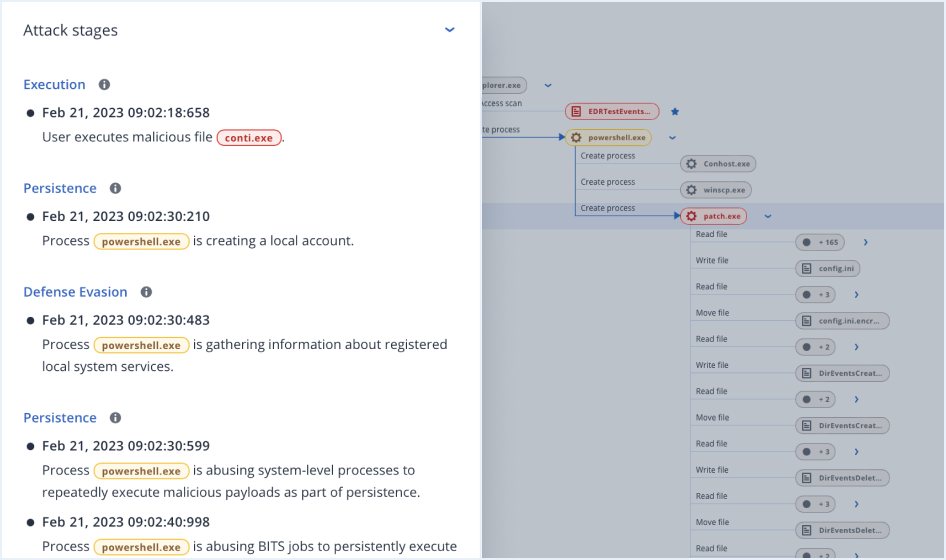
- RespondAnalyze incidents with speed guided by AI and respond with a single click to: investigate and contain cybersecurity threats; remediate, rollback, and recover from attacks; close vulnerability gaps.
- RecoverDeliver unmatched data protection and business continuity with no data loss across your clients’ IT stack.
Streamline your services and reduce resource requirements with AI-based innovations
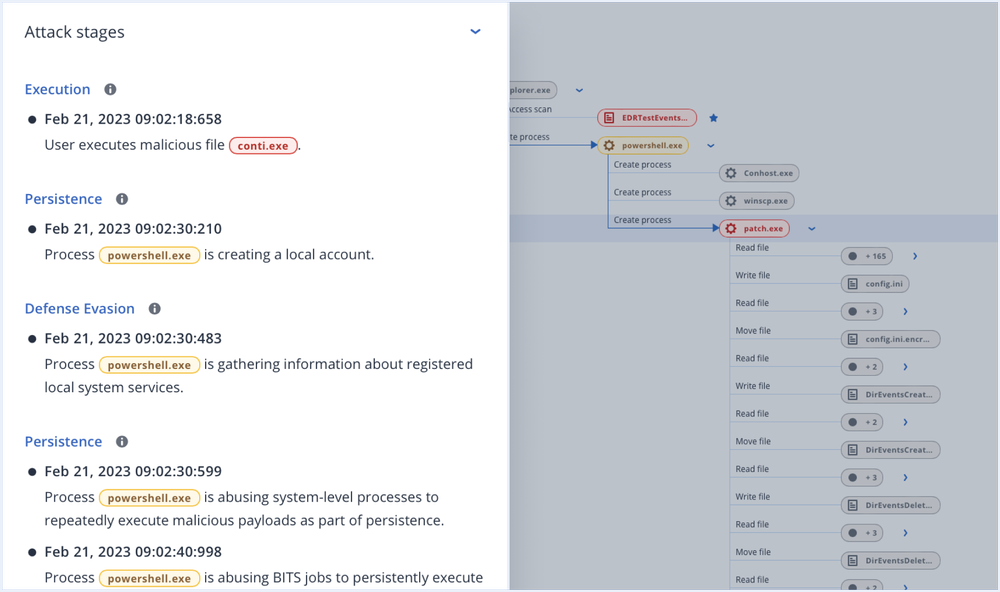
- AI-guided, minutes-not-hours attack analysisLeverage AI-based incident summaries and interpretations aligned with MITRE ATT&CK framework to unlock a swifter response.
- Single-click response to incidentsEnsure faster mean-time-to-response (MTTR) by isolating and remediating the threat, recovering from the damage, and closing open security gaps via a single-click response.
- Prioritized view of incidentsEnsure you always stay on top of high-risk activities with a prioritized view of incidents, rather than a flat list of alerts.
Soluções premiadas de proteção cibernética











Acronis Cyber Protect Cloud with Advanced Security + XDR
See Acronis XDR in action — a complete, natively integrated, highly efficient protection solution built for MSPs
Consolidation and service management centralization with Acronis is easier and more approachable than ever. Expand your capabilities to offer holistic protection, defend organizations, and provide true business resilience for clients and their data in the face of modern cyber threats.
| Behavior-based detection | | |
| Anti-ransomware protection with automatic rollback | | |
| Vulnerability assessments | | |
| Device control | | |
| File- and system-level backup | | |
| Inventory collection (with Advanced Management) | | |
| Patch management (with Advanced Management) | | |
| #CyberFit Score (security posture evaluation) | | |
| Remote connection (with Advanced Management) | | |
| Remediation including full reimaging | | |
| Business continuity (with Advanced Disaster Recovery) | | |
| URL filtering | | |
| Exploit prevention | | |
| Real-time threat intelligence feed | | |
| Automated, tunable allowlisting based on profiling | | |
| Forensic data collection | | |
| Event monitoring | | |
| Automated event correlation | | |
| Prioritization of suspicious activities | | |
| AI-generated incident summaries | | |
| Automated MITRE ATT&CK® attack chain visualization and interpretation | | |
| Single-click response to incidents | | |
| Full threat containment including endpoint quarantine and isolation | | |
| Intelligent search for IoCs including emerging threats | | |
| Attack-specific rollback | | |
Próximos eventos on-line
Expanda seus serviços com pacotes de proteção avançados
Acrescente outros componentes poderosos para reforçar ainda mais os seus serviços com pacotes de proteção avançados e capacidades de proteção cibernética exclusivas. Controle os seus custos pagando apenas pelas funcionalidades de que seus clientes necessitam. Os pacotes Advanced incluem:
- Advanced Security + EDRO Acronis EDR, desenvolvido para provedores de serviços, permite simplificar a segurança de endpoint — detectando, analisando e remediando rapidamente ataques avançados enquanto assegura uma continuidade de negócios inigualável. Elimine o custo e a complexidade de vários produtos isolados e capacite a sua equipe com uma única solução completa de proteção cibernética, simples de gerenciar e de implantar.
- Priorização de incidentes de segurança
- Interpretações de ataque orientadas por inteligência artificial
- Continuidade de negócios com backup e recuperação integrados
- Advanced ManagementFacilite o gerenciamento de vulnerabilidades e feche prontamente quaisquer lacunas na infraestrutura de TI dos clientes por meio de gerenciamento de patches. Obtenha visibilidade sobre o inventário de software e melhore a disponibilidade monitorando as condições das unidades de disco. Facilite a administração de TI com relatórios agendados.
- Gerenciamento de patches
- Aplicação de patches à toda prova
- Monitoramento das condições dos discos rígidos
- Advanced AutomationSimplifique os negócios do MSP com uma plataforma única e integrada que automatiza fluxos de trabalho, melhora as interações com os clientes e oferece insights de negócios em tempo real. Viabilize decisões orientadas por dados e uma utilização mais inteligente dos recursos, resultando em uma gerenciabilidade melhor e em relacionamentos com os clientes baseados em valor.
- Automação de alto desempenho
- Previsões precisas
- Lucratividade de nível mais alto
- Advanced BackupReforce a proteção de dados oferecida aos clientes assegurando que não haja perda de dados, nem mesmo entre backups agendados. Estenda as capacidades de backup a SAP HANA, Oracle DB e clusters de aplicativos. Provedores de serviços também podem obter visibilidade do status de proteção de todos os dados na infraestrutura dos clientes.
- Proteção de dados contínua
- Mapa de proteção de dados
- Relatórios de backup agendados
- Advanced Disaster RecoveryTenha seus clientes de volta ao trabalho em questão de minutos subindo sistemas instantaneamente no Acronis Cloud e restaurando-os em qualquer lugar, garantindo disponibilidade de dados imediata. Torne a recuperação de desastres indolor e aumente a eficiência com coordenação, runbooks e failover automático.
- Coordenação da recuperação de desastres
- Failover de produção
- VPN de site para site
- Advanced Email SecurityBloqueie qualquer ameaça em e-mails, inclusive spam, phishing, comprometimento de e-mail corporativo (BEC), ameaças persistentes avançadas (APTs) e ataques de dia zero em questão de segundos, antes que os usuários finais sejam atingidos. Aproveite a tecnologia de nova geração da Perception Point para detecção ultrarrápida e facilidade de distribuição, configuração e gerenciamento.
- Mecanismos antiphishing e antispoofing
- Tecnologias antievasão
- Detecção dinâmica de nova geração contra ataques de dia zero
- Advanced File Sync and ShareObtenha controle total sobre a localização, o gerenciamento e a privacidade dos dados com um serviço de sincronização e compartilhamento de arquivos, incluindo um livro de transações para permitir reconhecimento de firma e recursos de assinatura eletrônica, em todas as plataformas.
- Reconhecimento de firma do arquivo
- Assinaturas eletrônicas incorporadas
- Verificação de arquivo independente
Saiba mais, ganhe mais com Acronis Academy
Se você e sua equipe estão buscando certificações profissionais ou iniciando um negócio MSP, estamos aqui para apoiá-lo em todas as etapas.

Comece a aprender gratuitamente
A MSP Academy foi criada para oferecer treinamento neutro em relação a fornecedores, cobrindo o A a Z do gerenciamento de um negócio.
Certifique-se
A Acronis Academy liberou o acesso a cursos e certificações de e-learning de alta qualidade que capacitam indivíduos e MSPs a aumentar suas habilidades e conhecimentos de segurança cibernética.
Faça login no Partner Portal
Os parceiros da Acronis potencializam seus negócios por meio do acesso completo aos recursos de treinamento transformadores da Acronis Academy. Explore nossa extensa biblioteca educacional de serviços gerenciados no Portal do Parceiro!
Frequently Asked Questions
What is extended detection and response (XDR)?
XDR, or extended detection and response, refers to cybersecurity solutions that deliver comprehensive protection by integrating and correlating telemetry data and threat intelligence from multiple sources, including endpoints, email, identity, network, etc. This approach enables extended detection and response capabilities more holistically addressing threats beyond the endpoint by integrating data from multiple sources with security analytics to provide context, correlate security alerts, enable fast analysis and swift response — across diverse IT systems.
Why is providing an XDR-based service important?
Nowadays, threats are shifting their focus beyond the endpoint due to the high degree of SaaS-based and IoT infrastructure and remote work practices. This means the security perimeter itself is growing beyond the narrower endpoint focus, which was the standard in last years.
To counter these disperse risks and threats across multiple attack vectors such as endpoints, email, identity, etc., service providers have to deliver XDR-based services to their clients, especially ones working in high-risk industries such as finance, health care, legal, etc. — regardless of their size.
What are the benefits of using an XDR?
Extended detection and response solutions enable you with broader visibility on threats and attacks showing not only what has happened on the endpoint, but also integrating telemetry from other sources such as email, identity, cloud apps and network, to show you in much greater detailed how an attack originated, got in, progressed, and what damage it has done.
This enables faster analysis at scale for incidents without having to manually correlate events between different point cybersecurity solutions.
Moreover, XDR enables you to swiftly perform remediation actions that are not purely focused on isolating the endpoint and removing the threat from it, but also enable further risk mitigation and remediation capabilities such as blocking malicious attachments in emails, blocking malicious email addresses, terminating user account sessions, suspending user accounts, etc.
This comprehensive approach to cybersecurity not only ensures the highest level of protection against advanced threats and targeted attacks, reducing the risks for clients, but can also support compliance and help you streamline incident investigation and remediation efforts that are insurmountable with point security solutions.
What is the difference between EDR and XDR?
Endpoint detection and response, or EDR, is focused on providing event correlation, contextual information and analysis and a response toolkit for threats and attacks that are focused on the endpoint.
Extended detection and response, or XDR, goes the extra mile to ensure a more holistic approach to detection and response which goes beyond the endpoint, integrating data from other attack vectors such as email, identity, cloud applications or network. This approach further reduces risks and ensures a more complete protection that spans beyond the endpoint.
How to choose an XDR?
There’s a great variety of XDR solutions on the market, but the hard truth is that a majority of those have been created with enterprises in mind — introducing insurmountable complexity, costs, resource requirements and time-to-value for service providers.
When MSPs are considering what type of XDR to utilize, they should be thinking of capabilities that enable the MSP to deliver services on top of the solution to disperse and diverse client environments with minimal effort — such as SaaS management console, role-based access, multitenancy and ticketing integrations.
Moreover, as a service provide you need to think of scalability; can you deliver services on top of the XDR solution with your existing resources and would attracting more business also lead to higher resource requirements and costs? Innovations such as AI-guided attack analysis, generative AI experience and single-click response to incidents, along with native solution integrations beyond standard cybersecurity capabilities as well as the support by an MDR service, can help streamline your services, and reduce costs, resource requirements and time to value.
Sorry, your browser is not supported.
It seems that our new website is incompatible with your current browser's version. Don’t worry, this is easily fixed! To view our complete website, simply update your browser now or continue anyway.